SharkBot malware disguises itself as an antivirus on the Google Play Store
NCC Group experts reported on the SharkBot malware, which was found in the Google Play Store and which disguises itself as an antivirus, actually stealing money from users who installed the application.
SharkBot, like its counterparts TeaBot, FluBot, and Oscorp (UBEL), belongs to the category of banking Trojans capable of stealing credentials from hacked devices and bypassing multi-factor authentication mechanisms. Malware first appeared on the scene in November 2021.
A distinctive feature of SharkBot is its ability to perform unauthorized transactions through automatic transfer systems (ATS), that distinguishes it from, for example, TeaBot, which requires a live operator to interact with infected devices to perform malicious actions.
In this case, attackers use ATS to fool fraud detection systems by imitating the sequence of actions that a real user should perform, such as button presses, clicks, and gestures, necessary to make a money transfer.
Discovered in the Google Play Store on February 28, 2022, the malware was a series of dropper apps that used the Android Direct Reply feature to spread to other devices, making SharkBot the second banking trojan after FluBot to use this distribution method and have the capabilities of a worm.
In addition, SharkBot is multifunctional and allows an attacker to inject overlays on top of real banking applications and thus steal credentials, intercept keystrokes and establish complete remote control over devices. But all this becomes possible only if the victim gives the malware the right to use Accessibility Services.
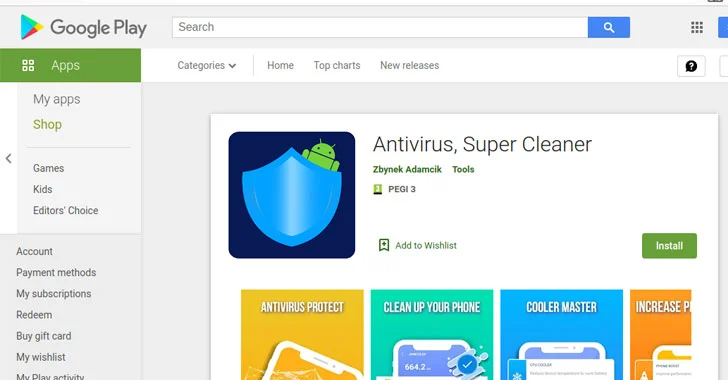
The malware hid in the following apps, which were installed more than 57,000 times in total:
- Antivirus, Super Cleaner (com.abbondioendrizzi.antivirus.supercleaner) – 1000+ installs;
- Atom Clean-Booster, Antivirus (com.abbondioendrizzi.tools.supercleaner) – 500+ installs;
- Alpha Antivirus, Cleaner (com.pagnotto28.sellsourcecode.alpha) – 5000+ installs;
- Powerful Cleaner, Antivirus (com.pagnotto28.sellsourcecode.supercleaner) – 50,000+ installs.
Let me remind you that we also reported that Fake antivirus promised protection from Pegasus spyware, but turned out to be a Trojan, and also that Thousands of Android Apps Leak Data Due to Misconfigured Firebase.