Researchers Find RCE Vulnerability on VirusTotal
Cysource experts discovered an RCE vulnerability that allowed “remotely executing commands on the VirusTotal platform and accessing various scanning capabilities.”
The researchers say that the bug was discovered a year ago, in April 2021, but Google, which owns VirusTotal, only recently gave permission to publish information about the vulnerability.

Marlon Fabiano da Silva
Let me remind you that we also said that RCE vulnerability was fixed in Sophos Firewall, and also that Expert Investigated Vulnerability in Snort Intrusion Prevention System.
The attack on VirusTotal was possible by uploading a specially crafted DjVu file through a web user interface. Such a file could be used to launch an exploit related to ExifTool, an open source utility used to read and edit EXIF metadata in images and PDF files.
At the root of the problem found by experts is a bug, which received the identifier CVE-2021-22204 (7.8 points on the CVSS scale) and represents the execution of arbitrary code that occurs due to incorrect handling of ExifTool with DjVu files. This issue was fixed back in April 2021.
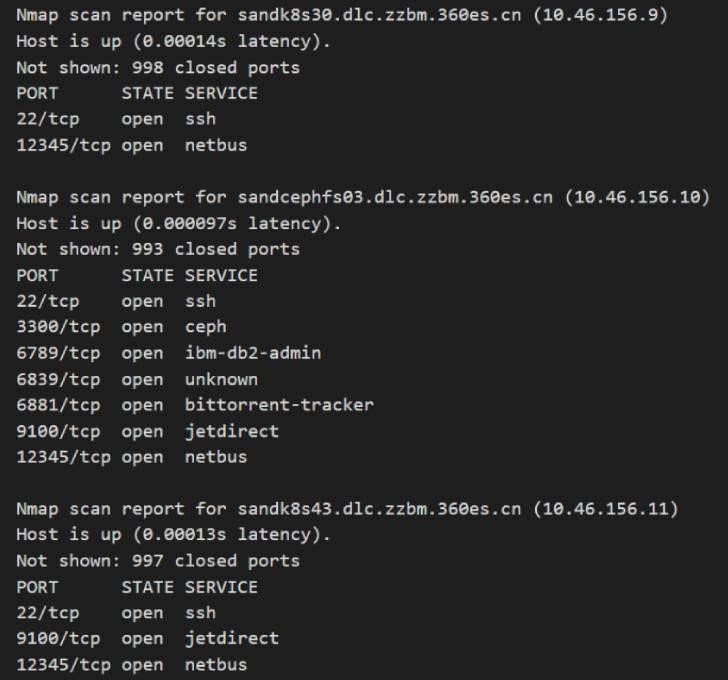
In their report, the experts write that the exploitation of this vulnerability in the context of VirusTotal provided not only access to an environment controlled by Google, but also gave privileged access to 50+ internal hosts.
Currently, the vulnerability has already been fixed, and VirusTotal no longer allows penetration into the Google infrastructure.












