Google Authenticator Will Have End-to-End Encryption
Earlier this week, Google announced that the Google Authenticator app would finally have cloud backup and cross-device syncing, but security experts noticed that the data was not end-to-end encrypted when it was uploaded to Google’s servers.
Let me remind you that we also wrote that Search for Random Leaks of API Keys, Passwords and Tokens Works for All GitHub Users, and also that OpenAI Introduced a Tool for Detecting Text Generated by Artificial Intelligence.
As you know, one of the most serious drawbacks of Google Authenticator has always been the lack of backup of one-time two-factor authentication (2FA) codes, as well as the lack of support for multiple devices at once.
By the way, the media reported that Cerberus Android Banker Steals 2FA Codes from Google Authenticator.
As a result, it turned out that having lost the device or losing access to it, the user was deprived of access to all accounts protected by this 2FA method, and restoring access became very difficult or impossible. It was also impossible to add 2FA codes to multiple devices without a cloud backup.
Now, these shortcomings have finally been fixed, but shortly after the company announced the introduction of cloud synchronization in Google Authenticator, security researchers from Mysk discovered that data was not end-to-end encrypted when uploaded to Google servers.
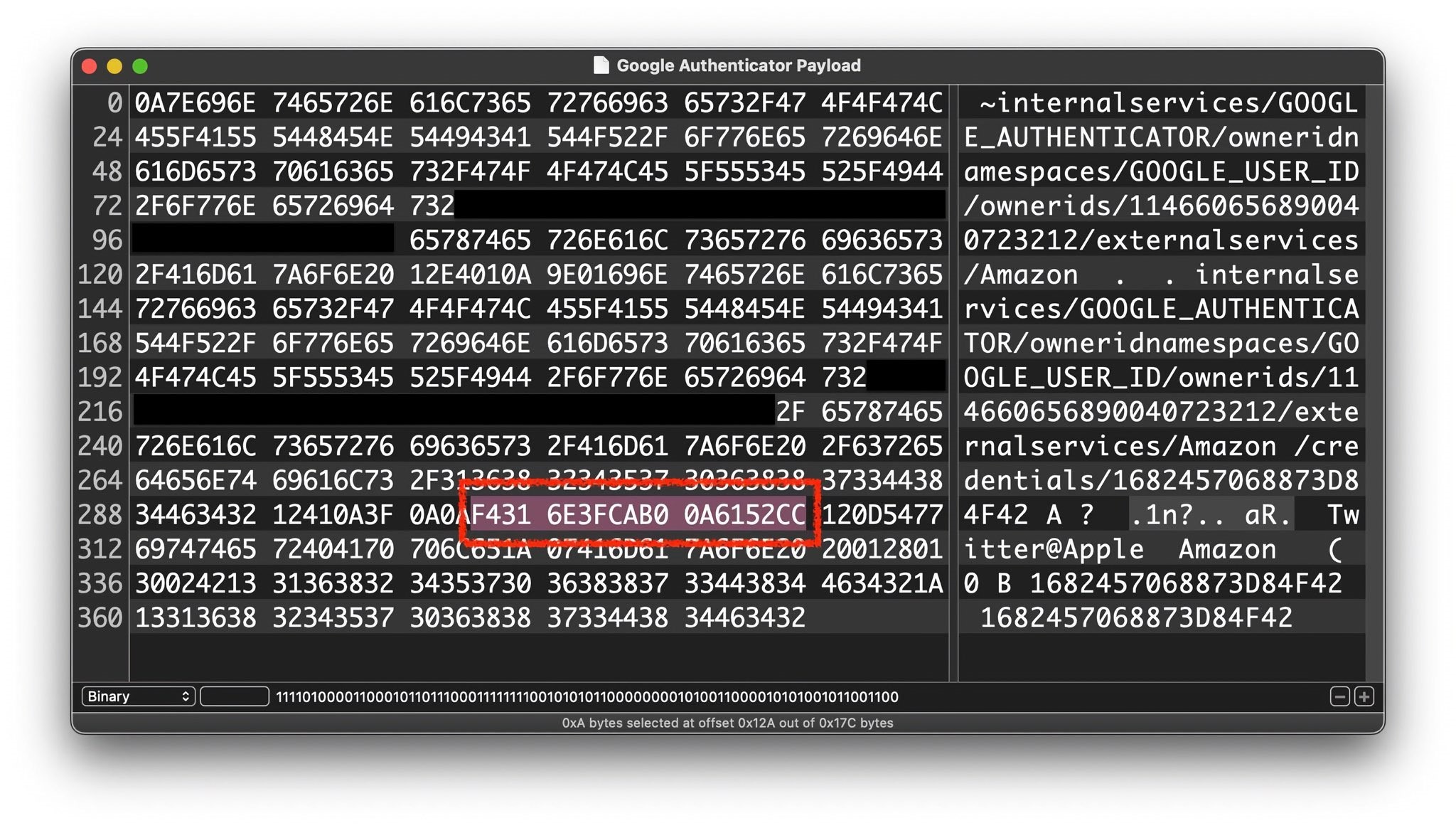
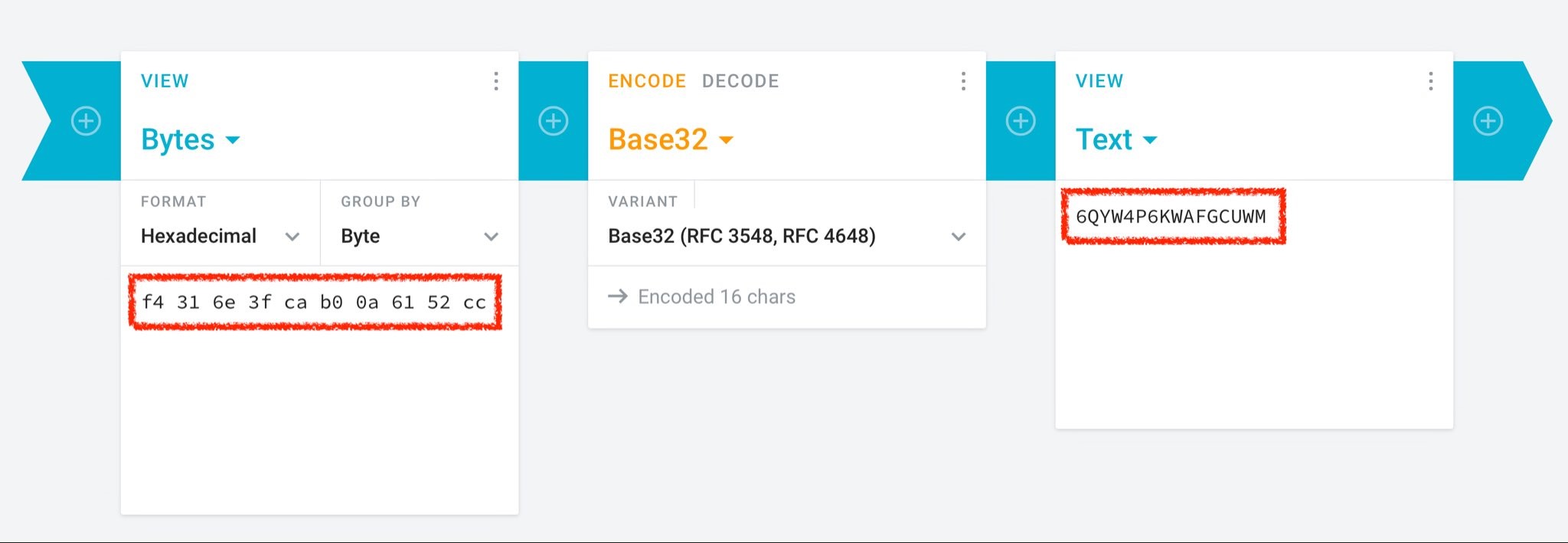
Since Google Authenticator does not offer end-to-end encryption, the data is stored on Google servers in a format that unauthorized parties can access (it can be either a Google hack or the actions of an unscrupulous employee).
Google developers reacted to this statement of information security experts quite quickly, saying that they would definitely add end-to-end encryption to the next versions of Google Authenticator.
A company representative explained to Bleeping Computer that developers are afraid that end-to-end encryption can completely block their own data, so the company is trying to implement such functions very carefully.