Microsoft-Approved UEFI Bootloaders Could Bypass Secure Boot
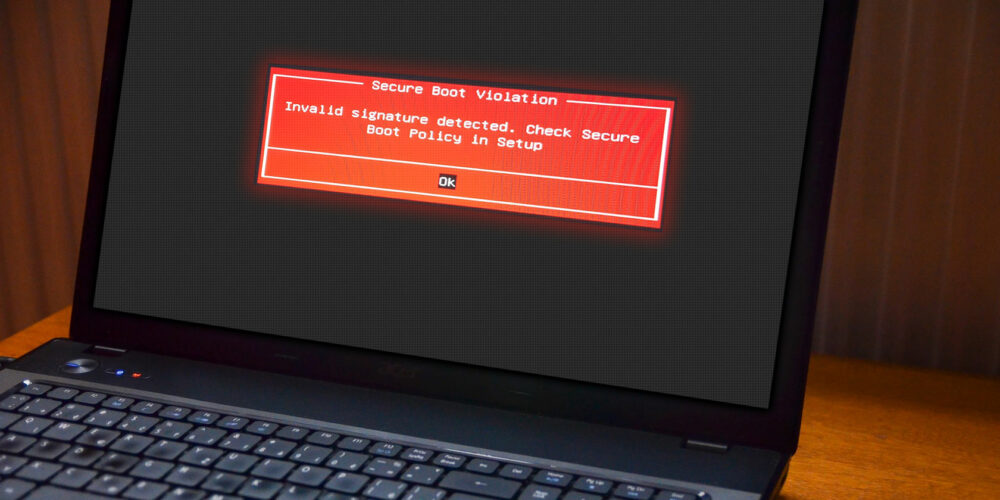
Eclypsium experts have discovered that a number of third-party UEFI bootloaders can be used to bypass UEFI Secure Boot protection, allowing attackers to execute malicious code before the operating system boots.
Let me remind you that we also said that Zloader Trojan Disables Microsoft Defender on Victims’ Systems.
The researchers remind that Secure Boot is part of the UEFI specification and is designed to protect the OS boot process so that only trusted code signed with a special certificate is executed within it.
Experts write that three Microsoft-approved UEFI bootloaders at once had vulnerabilities that allowed them to bypass Secure Boot and execute unsigned code:
- New Horizon Datasys Inc: CVE-2022-34302 (bypass Secure Boot via custom installer);
- CryptoPro Secure Disk: CVE-2022-34303 (bypassing Secure Boot via UEFI Shell);
- Eurosoft (UK) Ltd: CVE-2022-34301 (Secure Boot bypass via UEFI Shell).
Currently, Microsoft has already developed and released update KB5012170, which fixes problems in the listed bootloaders. “This update addresses the vulnerability by adding signatures of known vulnerable UEFI modules to DBX,” Microsoft said.
The Eclypsium report notes that using the Eurosoft and CryptoPro Secure Disk bootloaders, an attacker can bypass Secure Boot using signed UEFI shells (esdiags.efi and Shell_Full.efi). At the same time, it is emphasized that the exploitation of these vulnerabilities could be easily automated using scripts, although users could pay attention to the exploitation of bugs.
In the case of the New Horizon Datasys bootloader, the attack would be much more invisible to users. “This bootloader contains a built-in Secure Boot bypass that leaves Secure Boot enabled but disables checks,” the experts write. As a result, exploiting CVE-2022-34302 is much simpler than the other two bugs and allows you to disable Secure Boot by executing unsigned code directly. Researchers warn that hackers will certainly try to take advantage of this problem.
A security bulletin published by Carnegie Mellon University’s CERT states that early boot code can “also bypass conventional OS and EDR-based protections.” CERT experts list 23 UEFI bootloader vendors, and only three of them have clear status: Microsoft (affected), Phoenix Technologies (unaffected), and Red Hat (unaffected).
The other 20 vendors have been informed of the issues, but it is currently unknown if their products are affected. This list includes companies such as Acer, AMD, American Megatrends, ASUSTeK, DELL, Google, Hewlett Packard Enterprise, HP, Lenovo, Toshiba, and VAIO Corporation.